Fortify Your Digital Assets Against the Rising Tide of Cyber Risk
Security AuditFor high-growth web applications, security cannot be a reactive measure—it must be a foundational pillar of your technical roadmap. Many brand leaders live with the silent anxiety of “black box” vulnerabilities, unaware of the structural weaknesses that could derail their entire digital ecosystem. We provide a surgical, evidence-based audit of your web applications to identify and remediate risks before they can be exploited. By shifting from a “hope-based” security model to one rooted in hard data and continuous monitoring, we ensure your brand’s ascent is protected by a rigorous safety line of technical integrity.
Technical Precision

Strategic Alignment

Impactful Velocity

Vulnerability Scanning
We deploy sophisticated, non-intrusive scans that identify thousands of known vulnerabilities across your application’s surface area with surgical precision.
API Security
Our audits extend deep into your application’s logic, ensuring your API endpoints are secure and protected from unauthorized data exfiltration.
DevSecOps Integration
We bridge the gap between development and security, embedding automated checks into your CI/CD pipeline to ensure every deployment is secure by design.
Compliance Mapping
We align your technical infrastructure with global standards like GDPR, HIPAA, and SOC2, removing the guesswork from regulatory requirements.
Remediation Roadmapping
Beyond identifying risks, we provide a prioritized strategic roadmap with clear technical instructions for your team to close gaps effectively.
Security Monitoring
Secure your long-term ROI with recurring assessments that adapt to new threats, ensuring your application remains a fortress as you scale.
From Friction to Strategic Momentum
Most of our clients come to us at a breaking point where their technology has become an anchor rather than an engine. They are exhausted by the "thousand tiny decisions" that seem to lead nowhere and frustrated by partners who speak in jargon but deliver little impact. We exist to flip that script, replacing uncertainty with a high-performance framework that allows you to stop worrying about your website and start focusing on your market leadership.
Before

Stuck in a cycle of "putting out fires"
Stranded by agencies who disappeared
Exhausted by technical noise and jargon
After

Total confidence in a stable foundation
A clear roadmap with zero guesswork
A dedicated partner who actually answers
The Fuel Behind the Results
While we take our work incredibly seriously, we try not to take ourselves too seriously. These numbers represent the grit, the late nights, and the strategic wins we’ve accumulated over the years while building and protecting our clients' digital engines.
- 0
Cups of Coffee Downed
This is the high-octane fuel that powers our late-night triage sessions and ensures your "thousand tiny decisions" are made with 100% caffeine-backed precision.
- $0m
Client Revenue Managed
We don't just push pixels; we manage the complex marketing engines and ad spend that drive real-world growth and predictable, scalable revenue for our partners.
- 0+
Technical Issues Resolved
From repairing broken "legacy code" to optimizing complex API integrations, we have spent six years clearing the technical noise so your brand can perform.
Turning Technical Risk into Strategic Advantage
A secure application is a reliable application. In the enterprise landscape, security is often treated as a hurdle rather than a foundation, leading to stagnant growth and eroded customer trust. Our approach to security auditing is designed to provide total clarity for CEOs and CMOs who cannot afford the reputational damage of a breach. We move past superficial checks to perform a forensic analysis of your application’s architecture, ensuring that your growth is built on a stable, unshakeable foundation.
Structural IntegrityProactive Threat Mitigation
Waiting for a breach to occur is a gamble that high-end brands simply cannot take. We take a data-centric approach to threat mitigation, identifying OWASP Top 10 risks and logical flaws before they manifest as crises. This proactive stance eliminates the anxiety of the unknown, replacing it with a documented, evidence-based security posture that protects your brand’s most valuable digital assets. By securing your “anchor points” now, we ensure a safer and more predictable path to the summit.

Scalable Security Logic
As your web application evolves, so do the methods used by bad actors. Our audits are built to scale with your ambition, utilizing automated logic that keeps pace with rapid development cycles. We don’t just provide a snapshot in time; we provide the technical framework for ongoing resilience. This ensures that your internal teams can focus on innovation and scalability, knowing that the structural integrity of the platform is being monitored and maintained by an expert technical ally.

The Rigor Required for Total Protection
Vulnerability Forensics and Architectural Assessment are the dual anchors of our security practice. We don’t just find bugs; we understand the underlying logic that allowed them to exist, providing the deep-tier technical clarity required to prevent recurrence. By auditing the very “bone structure” of your web application, we ensure that your security measures are integrated into the codebase itself, rather than being treated as an external “black box” add-on.
Compliance Literacy and Remediation Strategy bridge the gap between technical risk and business leadership. We translate complex security vulnerabilities into clear, actionable roadmaps that your developers can follow and your stakeholders can understand. Combined with our Ethical Precision, these standards ensure that every audit we perform is conducted with the highest levels of integrity, providing you with a transparent and evidence-based view of your brand’s digital health.
Don't Climb Without a Safety Line
Strategic Security Guidance for the High-Growth Era.The frustration of being burned by “creative-only” agencies that ignore technical security is a common pain point for ambitious brand leaders. You need a partner who understands that security is not an obstacle to growth, but the very thing that makes growth possible. At TopOut Group, we act as your technical guide, providing the authoritative expertise and data-driven precision needed to move from a state of vulnerability to a position of total market confidence.
Eliminating "Black Box" Risks
We shine a light on the hidden vulnerabilities in your web applications that traditional audits miss. Our evidence-based reporting gives you a clear, prioritized list of risks to address immediately.
ROI-Focused Security
A secure platform is a scalable platform. By preventing downtime and data loss, we ensure your technical infrastructure remains a high-performing engine for your long-term success.
No Jargon, Just Answers
We know that navigating the digital landscape often feels like a series of "thousand tiny decisions" made in the dark. Whether you are curious about our specific technical stack or how our non-pushy sales process actually works, we believe in providing total clarity before we ever pick up a wrench. If you don't see your specific question here, we are always available for a candid conversation about your brand’s unique needs.
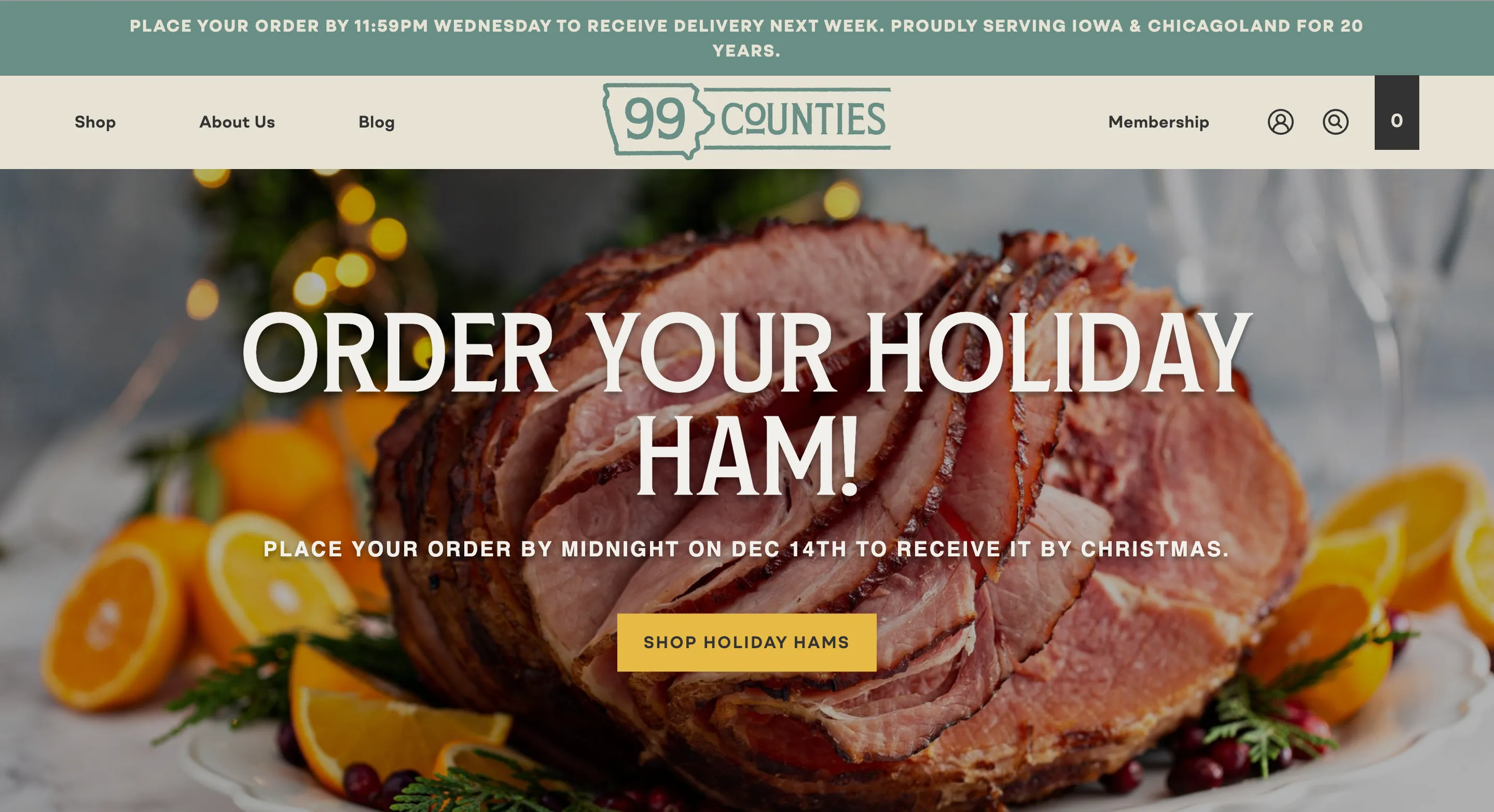
Our Strategies in Motion
Expertise is best measured by the challenges we have overcome and the systems we have stabilized. From rescuing orphaned roots.io builds to optimizing complex Shopify Plus storefronts, our portfolio showcases the real-world application of our "thousand tiny decisions" philosophy. These projects represent more than just clean code and high-converting marketing; they are the success stories of brands that stopped fighting their technology and started leveraging it for growth.